Efficiency Of Token Ring - GeeksforGeeks.
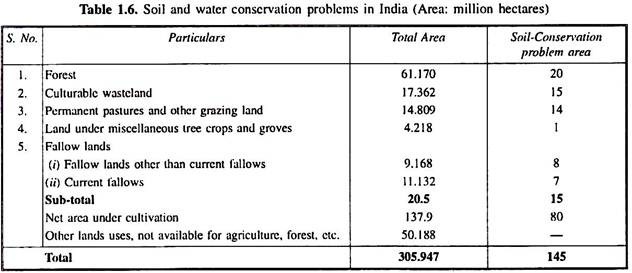
Ethernet vs. Token Ring Research Paper. Ethernet vs. Token Ring. Token ring (pic) Token ring local area network (LAN) technology is a local area network protocol which resides at the data link layer (DLL) of the OSI model. It uses a special three-byte frame called a token that travels around the ring. Token-possession grants the possessor permission to transmit on the medium. Token ring.Migrating from Token Ring essay. Place an order. Token-ring network emerged in the networking field in 1980s. In that era, it presented unsurpassed performance, reliability, as well scalability characteristics far overwhelming the capabilities of other local area networking technologies. However, during the recent decade, development in Ethernet technology has outdone the capabilities of token.Token Ring is a computer networking technology used to build local area networks.It uses a special three-byte frame called a token that travels around a logical ring of workstations or servers. This token passing is a channel access method providing fair access for all stations, and eliminating the collisions of contention-based access methods. There were several other earlier implementations.
IT 242 Week 4 CheckPoint Ethernet or Token Ring To purchase this material link IT 242 Week 4 CheckPoint Ethernet or Token Ring - Research Paper - Assignment07 Brainia.com.Token Ring supports two bandwidth options: 4Mbps and 16Mbps. Unlike Ethernet, Token Ring was designed to deal with the problem of collisions that occur when two stations transmit at the same time. This solution is accomplished by creating a closed ring and using an electronic “token,” which is passed around from host to host in the ring. Only the host that holds the token is allowed to.
Optimizing Performance of Token Ring for Bal-anced and Unbalanced Load Using OPNET Pankaj Rakheja, Dilpreet Kaur Abstract— Token Ring is a local area network which resides in the Data Link Layer (DLL) of the OSI model. Stations on a token ring LAN are logically organized in a ring topology with data being transmitted sequentially from one ring station to the next with a control token.